dube roger (28 resultados)
Filtros de b·squeda
Tipo de artĒculo
- Todos los tipos de productos
- Libros (28)
- Revistas y publicaciones (No hay ning·n otro resultado que coincida con este filtro.)
- C¾mics (No hay ning·n otro resultado que coincida con este filtro.)
- Partituras (No hay ning·n otro resultado que coincida con este filtro.)
- Arte, grabados y p¾sters (No hay ning·n otro resultado que coincida con este filtro.)
- FotografĒas (No hay ning·n otro resultado que coincida con este filtro.)
- Mapas (No hay ning·n otro resultado que coincida con este filtro.)
- Manuscritos y coleccionismo de papel (No hay ning·n otro resultado que coincida con este filtro.)
Condici¾n Mßs informaci¾n
- Nuevo (18)
- Como nuevo, Excelente o Muy bueno (4)
- Bueno o Aceptable (6)
- Regular o Pobre (No hay ning·n otro resultado que coincida con este filtro.)
- Tal como se indica (No hay ning·n otro resultado que coincida con este filtro.)
Encuadernaci¾n
Mßs atributos
- Primera edici¾n (4)
- Firmado (No hay ning·n otro resultado que coincida con este filtro.)
- Sobrecubierta (1)
- Con imßgenes (6)
- No impresi¾n bajo demanda (25)
Idioma (3)
Gastos de envĒo gratis
Ubicaci¾n del vendedor
Valoraci¾n de los vendedores
-
Elvis Aime Danser
Idioma: Francķs
Publicado por Diffusion du livre Mirabel (DLM), 2001
ISBN 10: 2890214621 ISBN 13: 9782890214620
Librería: Better World Books, Mishawaka, IN, Estados Unidos de America
EUR 26,93
Gastos de envĒo gratis
Se envĒa dentro de Estados Unidos de AmericaCantidad disponible: 1 disponibles
A±adir al carritoCondici¾n: Good. Pare, Roger Ilustrador. Former library copy. Pages intact with minimal writing/highlighting. The binding may be loose and creased. Dust jackets/supplements are not included. Includes library markings. Stock photo provided. Product includes identifying sticker. Better World Books: Buy Books. Do Good.
-
EUR 13,10
EnvĒo por EUR 10,00
Se envĒa de Alemania a Estados Unidos de AmericaCantidad disponible: 1 disponibles
A±adir al carritoCondici¾n: good. Befriedigend/Good: Durchschnittlich erhaltenes Buch bzw. Schutzumschlag mit Gebrauchsspuren, aber vollstõndigen Seiten. / Describes the average WORN book or dust jacket that has all the pages present.
-
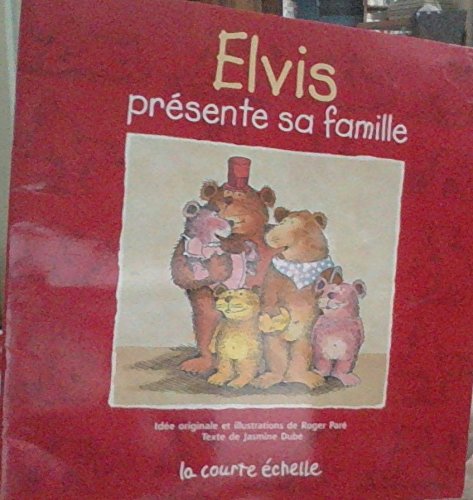
Elvis Presente Sa Famille (Elvis, 1) (French Edition)
Librería: Zoom Books East, Glendale Heights, IL, Estados Unidos de America
EUR 41,66
Gastos de envĒo gratis
Se envĒa dentro de Estados Unidos de AmericaCantidad disponible: 1 disponibles
A±adir al carritoCondici¾n: good. Book is in good condition and may include underlining highlighting and minimal wear. The book can also include "From the library of" labels. May not contain miscellaneous items toys, dvds, etc. . We offer 100% money back guarantee and 24 7 customer service.
-
EUR 41,70
Gastos de envĒo gratis
Se envĒa dentro de Estados Unidos de AmericaCantidad disponible: 1 disponibles
A±adir al carritoCondici¾n: Good. Former library copy. Pages intact with minimal writing/highlighting. The binding may be loose and creased. Dust jackets/supplements are not included. Includes library markings. Stock photo provided. Product includes identifying sticker. Better World Books: Buy Books. Do Good.
-
EUR 19,90
EnvĒo por EUR 22,00
Se envĒa de Belgica a Estados Unidos de AmericaCantidad disponible: 2 disponibles
A±adir al carritoCondici¾n: new. Livraison rapide, bien emballķ, service client soignķ.Pour tout renseignement complķmentaire, n'hķsitez pas Ó nous contacter.
-
Presto & Balthazar t.3 - la poule aux oeufs d'or
Librería: LiLi - La Libertķ des Livres, CANEJAN, Francia
EUR 6,63
EnvĒo por EUR 65,00
Se envĒa de Francia a Estados Unidos de AmericaCantidad disponible: 1 disponibles
A±adir al carritoCondici¾n: fine. l'article peut presenter de tres legers signes d'usure. vendeur professionnel; envoi soigne en 24/48h.
-
Hardware-based Computer Security Techniques to Defeat Hackers
Librería: PBShop.store UK, Fairford, GLOS, Reino Unido
EUR 116,87
EnvĒo por EUR 4,81
Se envĒa de Reino Unido a Estados Unidos de AmericaCantidad disponible: 15 disponibles
A±adir al carritoHRD. Condici¾n: New. New Book. Shipped from UK. Established seller since 2000.
-
Hardware-Based Computer Security Techniques to Defeat Hackers
Librería: GreatBookPrices, Columbia, MD, Estados Unidos de America
EUR 123,83
EnvĒo por EUR 2,30
Se envĒa dentro de Estados Unidos de AmericaCantidad disponible: Mßs de 20 disponibles
A±adir al carritoCondici¾n: New.
-
Hardware-based Computer Security Techniques to Defeat Hackers: From Biometrics to Quantum Cryptography (eng)
Librería: Brook Bookstore On Demand, Napoli, NA, Italia
EUR 116,45
EnvĒo por EUR 5,50
Se envĒa de Italia a Estados Unidos de AmericaCantidad disponible: Mßs de 20 disponibles
A±adir al carritoCondici¾n: new.
-
Hardware-Based Computer Security Techniques to Defeat Hackers
Librería: GreatBookPricesUK, Woodford Green, Reino Unido
EUR 116,85
EnvĒo por EUR 17,36
Se envĒa de Reino Unido a Estados Unidos de AmericaCantidad disponible: Mßs de 20 disponibles
A±adir al carritoCondici¾n: New.
-
Hardware-based Computer Security Techniques to Defeat Hackers: From Biometrics to Quantum Cryptography
Librería: THE SAINT BOOKSTORE, Southport, Reino Unido
EUR 138,50
EnvĒo por EUR 18,32
Se envĒa de Reino Unido a Estados Unidos de AmericaCantidad disponible: Mßs de 20 disponibles
A±adir al carritoHardback. Condici¾n: New. New copy - Usually dispatched within 4 working days.
-
Hardware-Based Computer Security Techniques to Defeat Hackers
Librería: Majestic Books, Hounslow, Reino Unido
EUR 155,24
EnvĒo por EUR 7,52
Se envĒa de Reino Unido a Estados Unidos de AmericaCantidad disponible: 3 disponibles
A±adir al carritoCondici¾n: New. pp. xxiii + 227 Illus.
-
Hardware-based Computer Security
Idioma: Inglķs
Publicado por John Wiley and Sons Ltd, 2008
ISBN 10: 0470193395 ISBN 13: 9780470193396
Librería: Kennys Bookshop and Art Galleries Ltd., Galway, GY, Irlanda
Original o primera edici¾n
EUR 155,78
EnvĒo por EUR 10,50
Se envĒa de Irlanda a Estados Unidos de AmericaCantidad disponible: Mßs de 20 disponibles
A±adir al carritoCondici¾n: New. Presents the primary hardware-based computer security approaches in an easy to read format. Provides comprehensive coverage of the primary hardware-based computer security approaches in a single, easy to use reference. Establishes a toolbox of core security issues of different approaches. Num Pages: 256 pages, Illustrations. BIC Classification: URY. Category: (P) Professional & Vocational. Dimension: 238 x 163 x 17. Weight in Grams: 478. . 2008. 1st Edition. Hardcover. . . . .
-
Hardware-Based Computer Security Techniques to Defeat Hackers
Librería: Books Puddle, New York, NY, Estados Unidos de America
EUR 170,05
EnvĒo por EUR 3,48
Se envĒa dentro de Estados Unidos de AmericaCantidad disponible: 3 disponibles
A±adir al carritoCondici¾n: New. pp. xxiii + 227.
-
Hardware-based Computer Security Techniques to Defeat Hackers (Hardcover)
Idioma: Inglķs
Publicado por John Wiley & Sons Inc, New York, 2008
ISBN 10: 0470193395 ISBN 13: 9780470193396
Librería: CitiRetail, Stevenage, Reino Unido
Original o primera edici¾n
EUR 133,47
EnvĒo por EUR 42,81
Se envĒa de Reino Unido a Estados Unidos de AmericaCantidad disponible: 1 disponibles
A±adir al carritoHardcover. Condici¾n: new. Hardcover. Presents primary hardware-based computer security approaches in an easy-to-read toolbox format Protecting valuable personal information against theft is a mission-critical component of today's electronic business community. In an effort to combat this serious and growing problem, the Intelligence and Defense communities have successfully employed the use of hardware-based security devices. This book provides a road map of the hardware-based security devices that can defeatand preventattacks by hackers. Beginning with an overview of the basic elements of computer security, the book covers: Cryptography Key generation and distribution The qualities of security solutions Secure co-processors Secure bootstrap loading Secure memory management and trusted execution technology Trusted Platform Module (TPM) Field Programmable Gate Arrays (FPGAs) Hardware-based authentification Biometrics Tokens Location technologies Hardware-Based Computer Security Techniques to Defeat Hackers includes a chapter devoted entirely to showing readers how they can implement the strategies and technologies discussed. Finally, it concludes with two examples of security systems put into practice. The information and critical analysis techniques provided in this user-friendly book are invaluable for a range of professionals, including IT personnel, computer engineers, computer security specialists, electrical engineers, software engineers, and industry analysts. Presents the primary hardware-based computer security approaches in an easy to read format. Provides comprehensive coverage of the primary hardware-based computer security approaches in a single, easy to use reference. Establishes a toolbox of core security issues of different approaches. Shipping may be from our UK warehouse or from our Australian or US warehouses, depending on stock availability.
-
HardwareBased Computer Security Techniques to Defeat Hackers From Biometrics to Quantum Cryptography
Librería: Revaluation Books, Exeter, Reino Unido
EUR 178,41
EnvĒo por EUR 11,57
Se envĒa de Reino Unido a Estados Unidos de AmericaCantidad disponible: 2 disponibles
A±adir al carritoHardcover. Condici¾n: Brand New. 1st edition. 256 pages. 9.25x6.00x0.75 inches. In Stock.
-
Hardware-based Computer Security
Idioma: Inglķs
Publicado por John Wiley and Sons Ltd, 2008
ISBN 10: 0470193395 ISBN 13: 9780470193396
Librería: Kennys Bookstore, Olney, MD, Estados Unidos de America
EUR 197,63
EnvĒo por EUR 9,16
Se envĒa dentro de Estados Unidos de AmericaCantidad disponible: Mßs de 20 disponibles
A±adir al carritoCondici¾n: New. Presents the primary hardware-based computer security approaches in an easy to read format. Provides comprehensive coverage of the primary hardware-based computer security approaches in a single, easy to use reference. Establishes a toolbox of core security issues of different approaches. Num Pages: 256 pages, Illustrations. BIC Classification: URY. Category: (P) Professional & Vocational. Dimension: 238 x 163 x 17. Weight in Grams: 478. . 2008. 1st Edition. Hardcover. . . . . Books ship from the US and Ireland.
-
Hardware-based Computer Security Techniques to Defeat Hackers (Hardcover)
Idioma: Inglķs
Publicado por John Wiley & Sons Inc, New York, 2008
ISBN 10: 0470193395 ISBN 13: 9780470193396
Librería: AussieBookSeller, Truganina, VIC, Australia
Original o primera edici¾n
EUR 205,29
EnvĒo por EUR 32,28
Se envĒa de Australia a Estados Unidos de AmericaCantidad disponible: 1 disponibles
A±adir al carritoHardcover. Condici¾n: new. Hardcover. Presents primary hardware-based computer security approaches in an easy-to-read toolbox format Protecting valuable personal information against theft is a mission-critical component of today's electronic business community. In an effort to combat this serious and growing problem, the Intelligence and Defense communities have successfully employed the use of hardware-based security devices. This book provides a road map of the hardware-based security devices that can defeatand preventattacks by hackers. Beginning with an overview of the basic elements of computer security, the book covers: Cryptography Key generation and distribution The qualities of security solutions Secure co-processors Secure bootstrap loading Secure memory management and trusted execution technology Trusted Platform Module (TPM) Field Programmable Gate Arrays (FPGAs) Hardware-based authentification Biometrics Tokens Location technologies Hardware-Based Computer Security Techniques to Defeat Hackers includes a chapter devoted entirely to showing readers how they can implement the strategies and technologies discussed. Finally, it concludes with two examples of security systems put into practice. The information and critical analysis techniques provided in this user-friendly book are invaluable for a range of professionals, including IT personnel, computer engineers, computer security specialists, electrical engineers, software engineers, and industry analysts. Presents the primary hardware-based computer security approaches in an easy to read format. Provides comprehensive coverage of the primary hardware-based computer security approaches in a single, easy to use reference. Establishes a toolbox of core security issues of different approaches. Shipping may be from our Sydney, NSW warehouse or from our UK or US warehouse, depending on stock availability.
-
Hardware-Based Computer Security Techniques to Defeat Hackers : From Biometrics to Quantum Cryptography
Librería: AHA-BUCH GmbH, Einbeck, Alemania
EUR 189,24
EnvĒo por EUR 62,74
Se envĒa de Alemania a Estados Unidos de AmericaCantidad disponible: 2 disponibles
A±adir al carritoBuch. Condici¾n: Neu. Neuware - Presents primary hardware-based computer security approaches in an easy-to-read toolbox formatProtecting valuable personal information against theft is a mission-critical component of today's electronic business community. In an effort to combat this serious and growing problem, the Intelligence and Defense communities have successfully employed the use of hardware-based security devices.This book provides a road map of the hardware-based security devices that can defeat-and prevent-attacks by hackers. Beginning with an overview of the basic elements of computer security, the book covers:\* Cryptography\* Key generation and distribution\* The qualities of security solutions\* Secure co-processors\* Secure bootstrap loading\* Secure memory management and trusted execution technology\* Trusted Platform Module (TPM)\* Field Programmable Gate Arrays (FPGAs)\* Hardware-based authentification\* Biometrics\* Tokens\* Location technologiesHardware-Based Computer Security Techniques to Defeat Hackers includes a chapter devoted entirely to showing readers how they can implement the strategies and technologies discussed. Finally, it concludes with two examples of security systems put into practice.The information and critical analysis techniques provided in this user-friendly book are invaluable for a range of professionals, including IT personnel, computer engineers, computer security specialists, electrical engineers, software engineers, and industry analysts.
-
Hardware-Based Computer Security Techniques to Defeat Hackers
Librería: GreatBookPricesUK, Woodford Green, Reino Unido
EUR 252,65
EnvĒo por EUR 17,36
Se envĒa de Reino Unido a Estados Unidos de AmericaCantidad disponible: Mßs de 20 disponibles
A±adir al carritoCondici¾n: As New. Unread book in perfect condition.
-
Hardware-based Computer Security Techniques to Defeat Hackers: From Biometrics to Quantum Cryptography
Librería: Mispah books, Redhill, SURRE, Reino Unido
EUR 243,13
EnvĒo por EUR 28,93
Se envĒa de Reino Unido a Estados Unidos de AmericaCantidad disponible: 1 disponibles
A±adir al carritoHardcover. Condici¾n: Like New. LIKE NEW. SHIPS FROM MULTIPLE LOCATIONS. book.
-
Hardware-Based Computer Security Techniques to Defeat Hackers
Librería: GreatBookPrices, Columbia, MD, Estados Unidos de America
EUR 279,81
EnvĒo por EUR 2,30
Se envĒa dentro de Estados Unidos de AmericaCantidad disponible: Mßs de 20 disponibles
A±adir al carritoCondici¾n: As New. Unread book in perfect condition.
-
L'╔ducation Poķtique: Illustrķe De 10 Hors-Texte En Camaieu
Publicado por Les Ateliers D'art Typographique, Montreal
Librería: Encore Books, Montreal, QC, Canada
EUR 101,48
EnvĒo por EUR 11,34
Se envĒa de Canada a Estados Unidos de AmericaCantidad disponible: 1 disponibles
A±adir al carritoSoft cover. Condici¾n: Very Good. Estado de la sobrecubierta: Very Good. Veillault, Roger Ilustrador. Wrappers crisp and clean, protected by mylar sleeve, block of text clean, binding tight, book in great condition.
-
EUR 1.058,32
EnvĒo por EUR 14,06
Se envĒa de Reino Unido a Estados Unidos de AmericaCantidad disponible: 1 disponibles
A±adir al carritopaperback. Condici¾n: Very Good. Most of our very good books have only minor imperfections such as shelf wear consistent with a new book that's sat on a bookshop shelf for a year or two. Occasionally we may miss other minor imperfections as we have to grade books at speed. Our books are dispatched from a Yorkshire former cotton mill. We list via barcode/ISBN so please note that the images are stock images and may not be the exact copy you receive, furthermore the details about edition and year might not be accurate as many publishers reuse the same ISBN for multiple editions and as we simply scan a barcode or enter an ISBN we do not check the validity of the edition data when listing. If you're looking for an exact edition please don't order (at least not without checking with us first, although we don't always have time to check). We aim to dispatch prompty, the service used will depend on order value and book size. We can ship to most countries, see our shipping policies. Payment is via Abe only.
-
Myfobrillogenesis (Cardiovascular Molecular Morphogenesis)
Publicado por Birkhauser, 2001
ISBN 10: 0817642269 ISBN 13: 9780817642266
Librería: Revaluation Books, Exeter, Reino Unido
EUR 158,35
EnvĒo por EUR 14,46
Se envĒa de Reino Unido a Estados Unidos de AmericaCantidad disponible: 2 disponibles
A±adir al carritoHardcover. Condici¾n: Brand New. 1st edition. 270 pages. 10.00x7.00x0.75 inches. In Stock.
-
Hardware-based Computer Security Techniques to Defeat Hackers (Hardcover)
Idioma: Inglķs
Publicado por John Wiley & Sons Inc, New York, 2008
ISBN 10: 0470193395 ISBN 13: 9780470193396
Librería: Grand Eagle Retail, Bensenville, IL, Estados Unidos de America
Original o primera edici¾n Impresi¾n bajo demanda
EUR 145,87
Gastos de envĒo gratis
Se envĒa dentro de Estados Unidos de AmericaCantidad disponible: 1 disponibles
A±adir al carritoHardcover. Condici¾n: new. Hardcover. Presents primary hardware-based computer security approaches in an easy-to-read toolbox format Protecting valuable personal information against theft is a mission-critical component of today's electronic business community. In an effort to combat this serious and growing problem, the Intelligence and Defense communities have successfully employed the use of hardware-based security devices. This book provides a road map of the hardware-based security devices that can defeatand preventattacks by hackers. Beginning with an overview of the basic elements of computer security, the book covers: Cryptography Key generation and distribution The qualities of security solutions Secure co-processors Secure bootstrap loading Secure memory management and trusted execution technology Trusted Platform Module (TPM) Field Programmable Gate Arrays (FPGAs) Hardware-based authentification Biometrics Tokens Location technologies Hardware-Based Computer Security Techniques to Defeat Hackers includes a chapter devoted entirely to showing readers how they can implement the strategies and technologies discussed. Finally, it concludes with two examples of security systems put into practice. The information and critical analysis techniques provided in this user-friendly book are invaluable for a range of professionals, including IT personnel, computer engineers, computer security specialists, electrical engineers, software engineers, and industry analysts. Presents the primary hardware-based computer security approaches in an easy to read format. Provides comprehensive coverage of the primary hardware-based computer security approaches in a single, easy to use reference. Establishes a toolbox of core security issues of different approaches. This item is printed on demand. Shipping may be from multiple locations in the US or from the UK, depending on stock availability.
-
HardwareBased Computer Security Techniques to Defeat Hackers From Biometrics to Quantum Cryptography
Librería: Revaluation Books, Exeter, Reino Unido
EUR 165,28
EnvĒo por EUR 11,57
Se envĒa de Reino Unido a Estados Unidos de AmericaCantidad disponible: 2 disponibles
A±adir al carritoHardcover. Condici¾n: Brand New. 1st edition. 256 pages. 9.25x6.00x0.75 inches. In Stock. This item is printed on demand.
-
Hardware-based Computer Security Techniques to Defeat Hackers: From Biometrics to Quantum Cryptography
Librería: THE SAINT BOOKSTORE, Southport, Reino Unido
EUR 169,25
EnvĒo por EUR 18,32
Se envĒa de Reino Unido a Estados Unidos de AmericaCantidad disponible: Mßs de 20 disponibles
A±adir al carritoHardback. Condici¾n: New. This item is printed on demand. New copy - Usually dispatched within 5-9 working days 508.